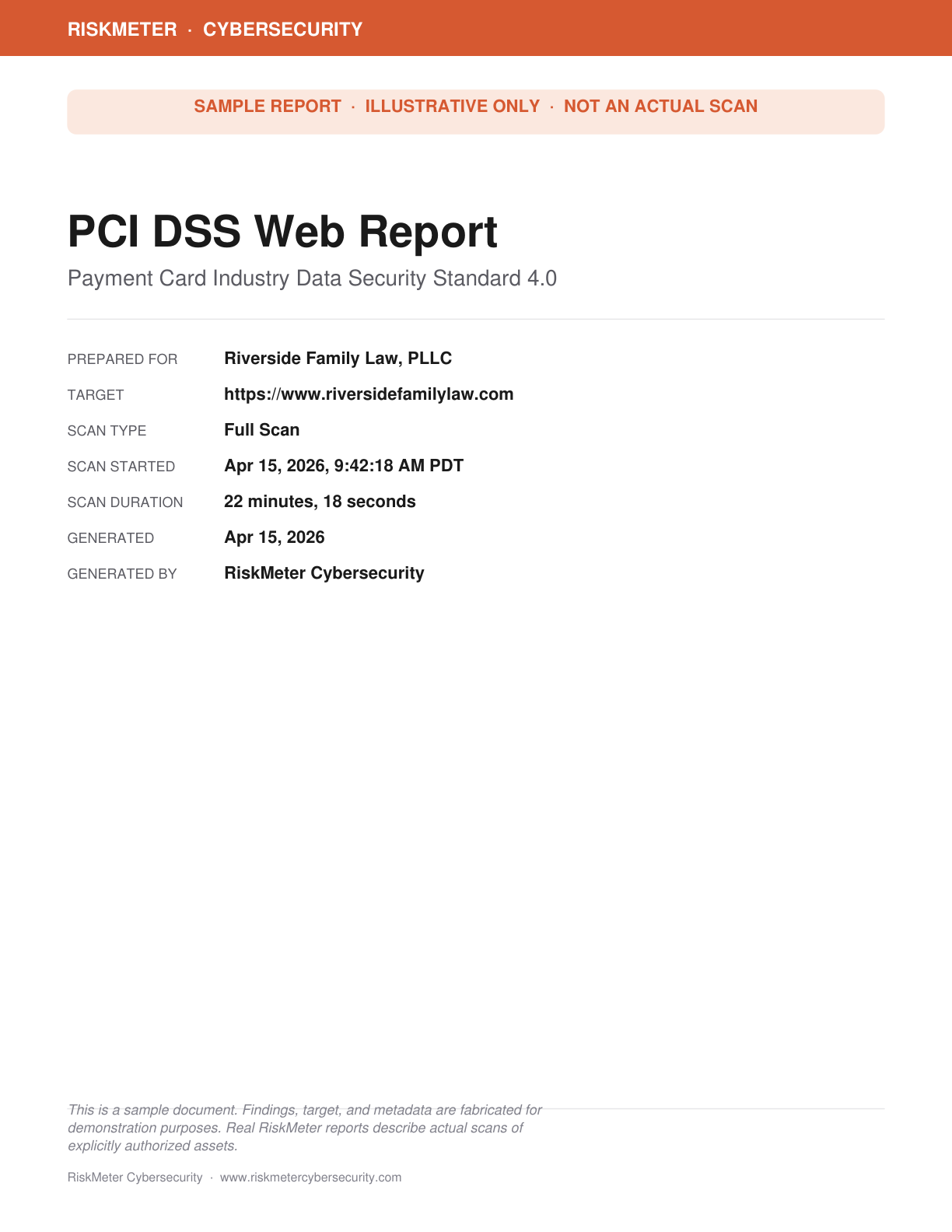
RiskMeter Website Security Report
The plain-English summary every RiskMeter customer receives. Threat level, scan detail, severity counts, and an executive list of every vulnerability group discovered — written so a non-technical reader can decide what to do next.
Designed to be readable by an owner, managing partner, or office manager — and forwardable to an insurance broker or institutional client without translation.
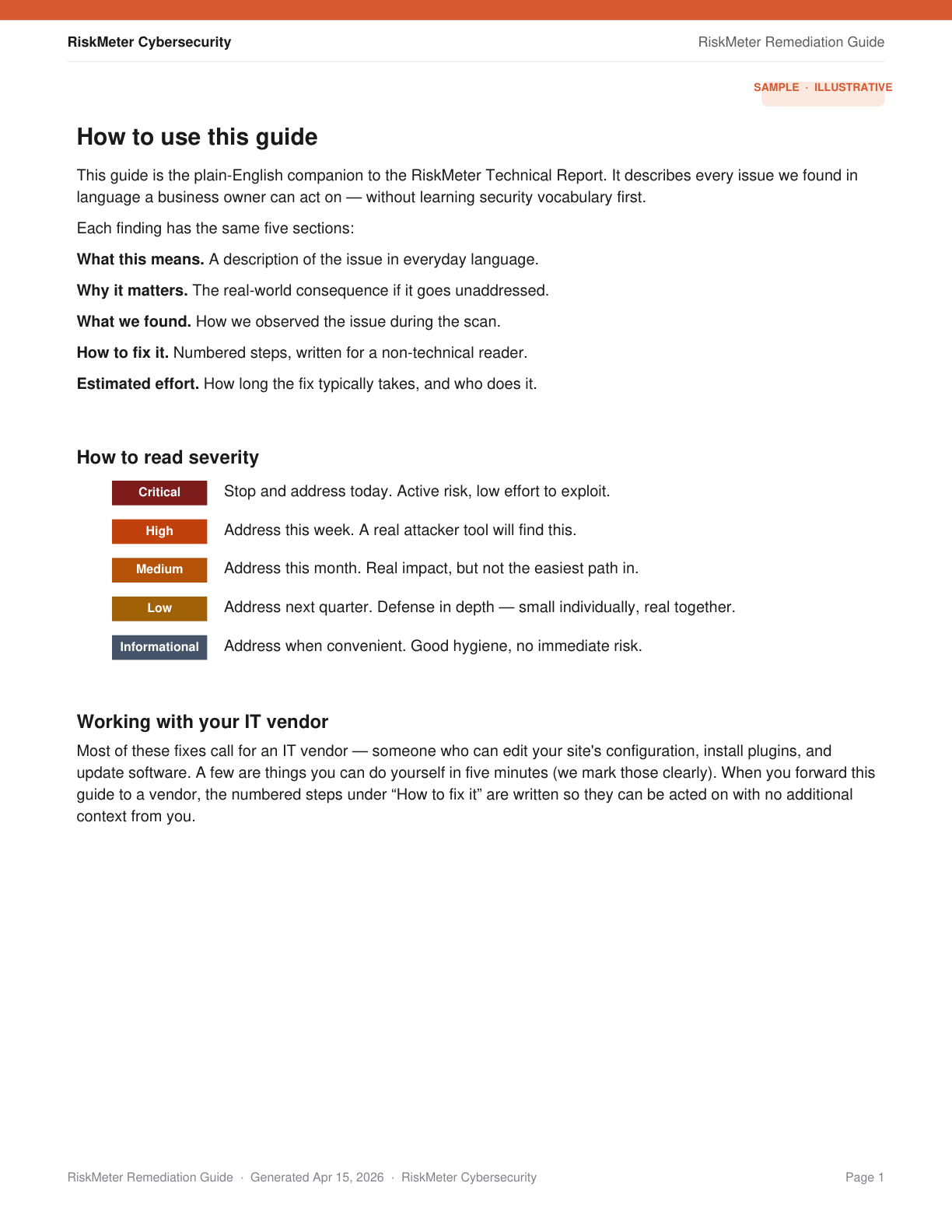
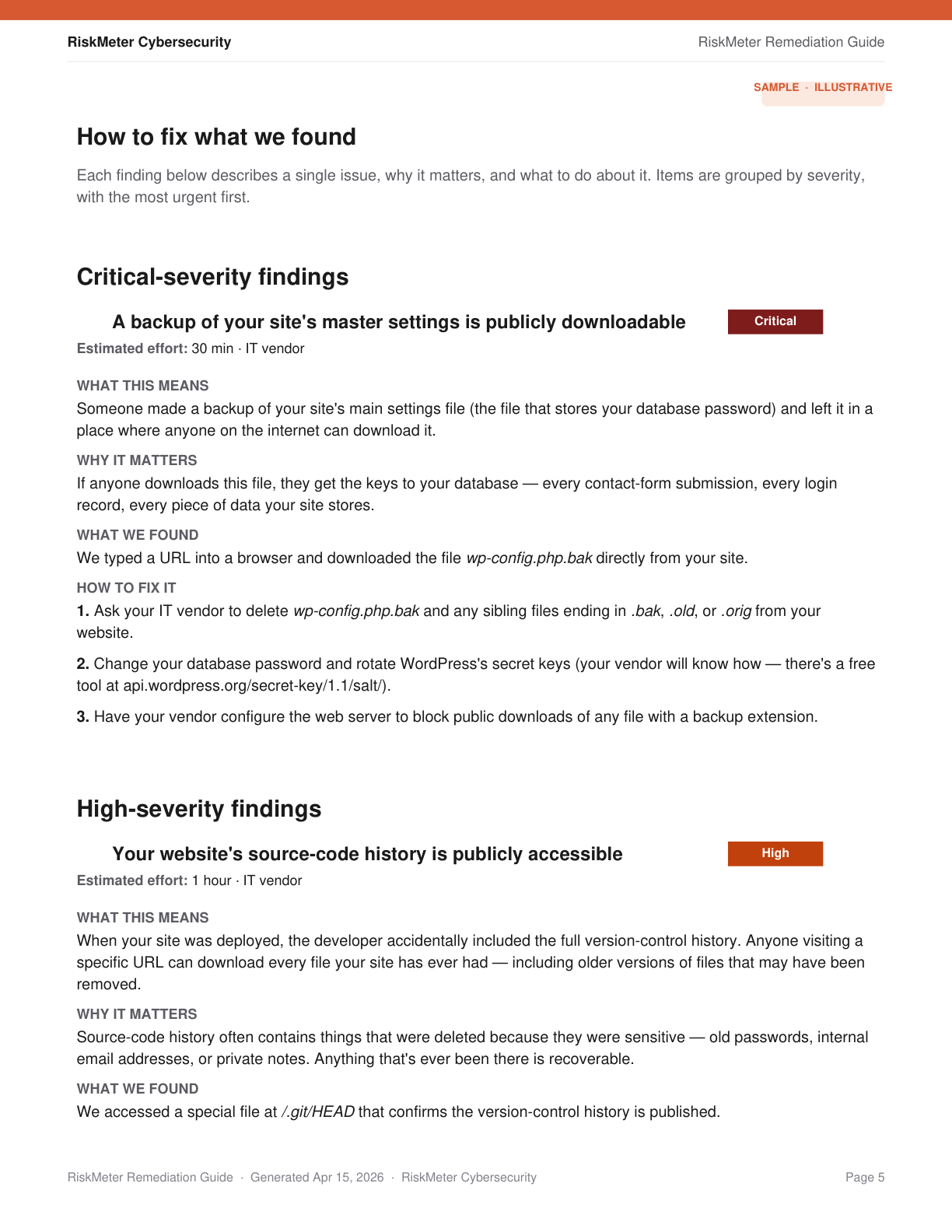
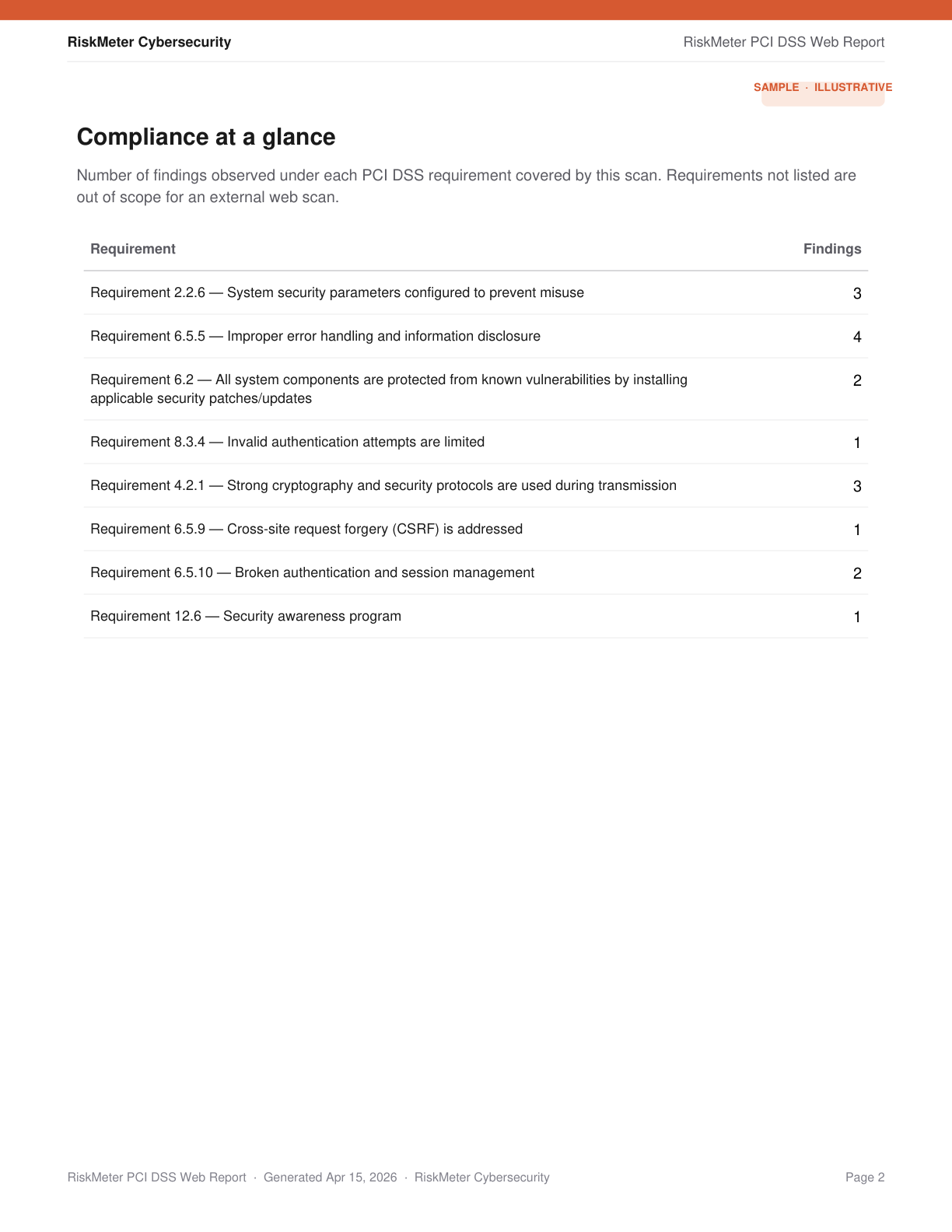
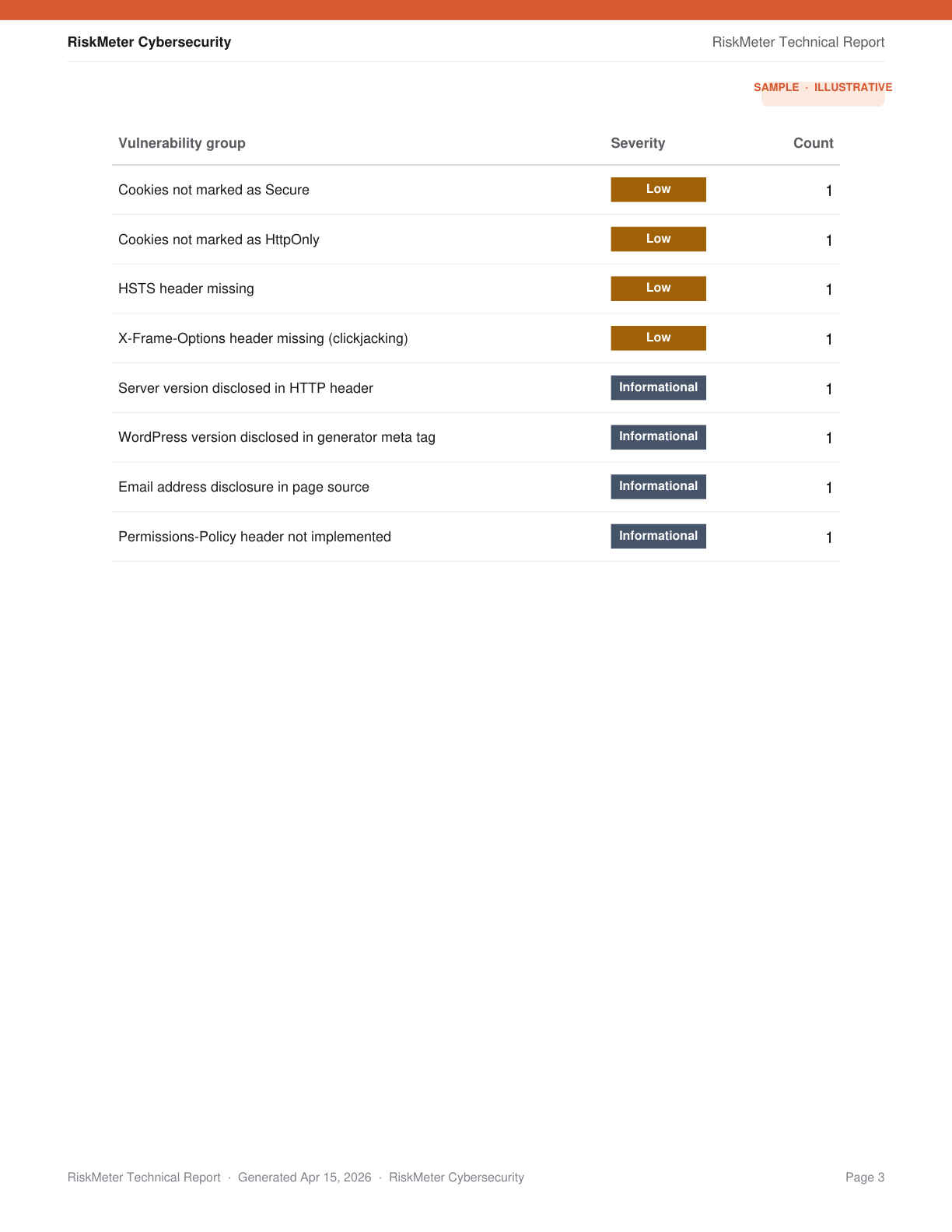
What's in this report
- Cover with target, scan window, and scan duration
- Overall threat level with a one-paragraph plain-English summary
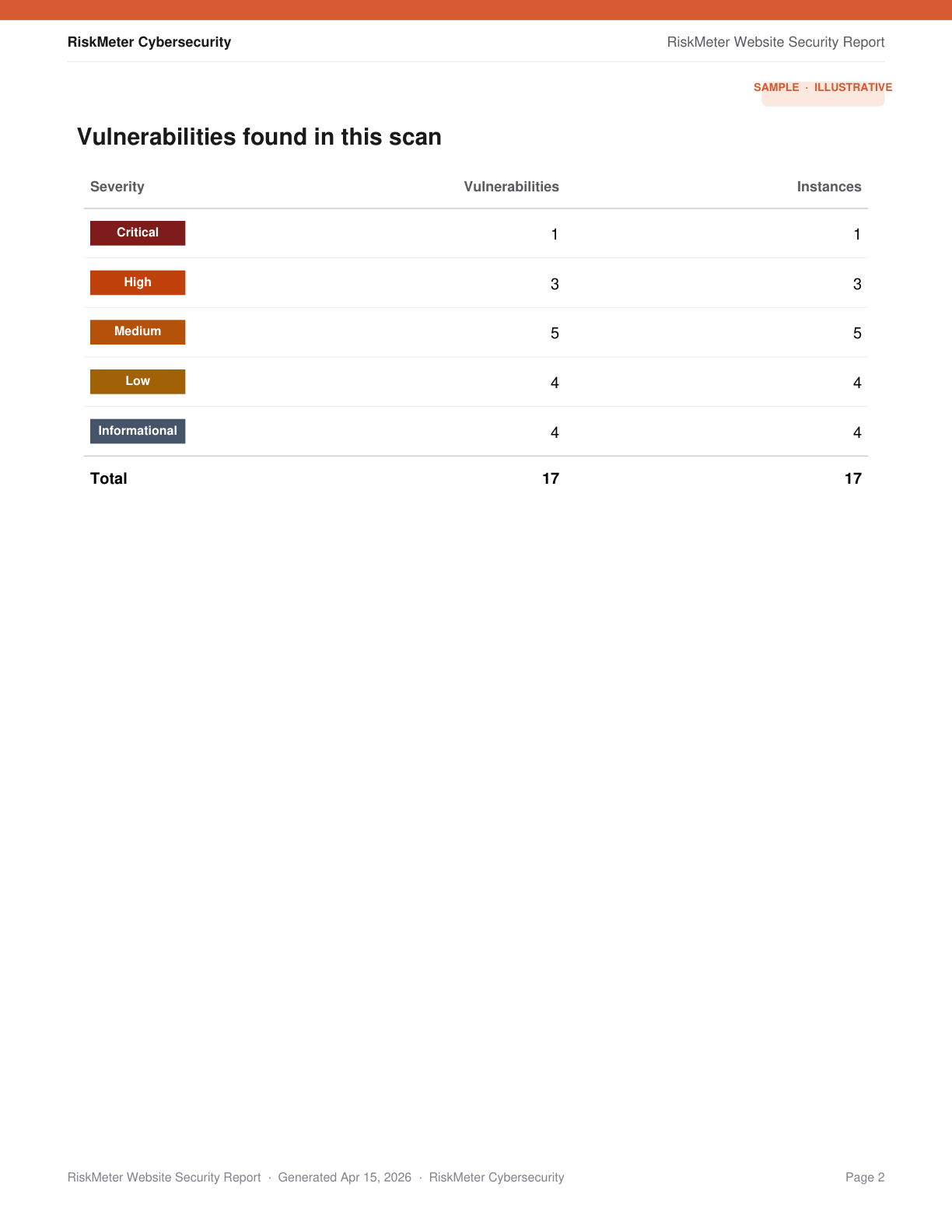
- Severity counts (Critical / High / Medium / Low / Informational)
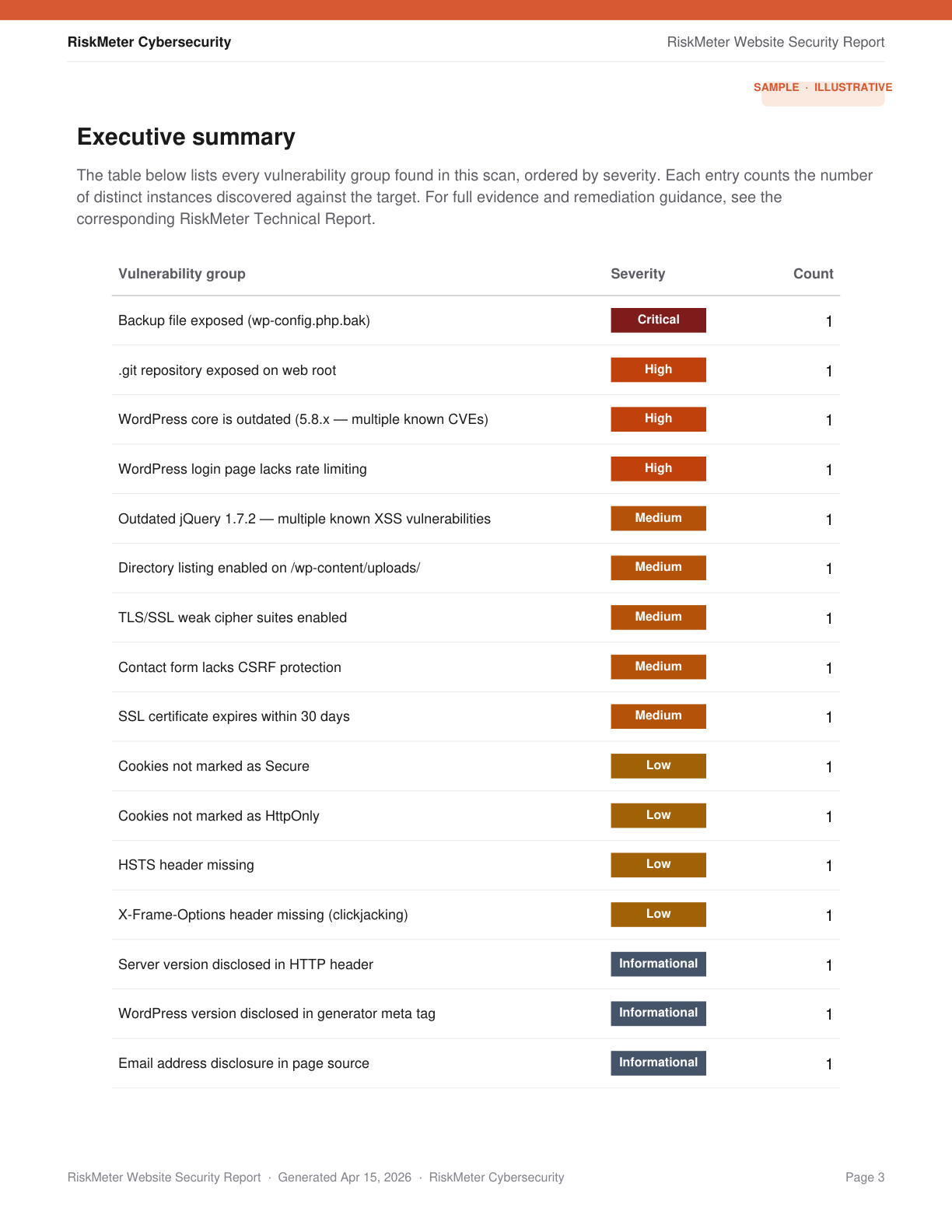
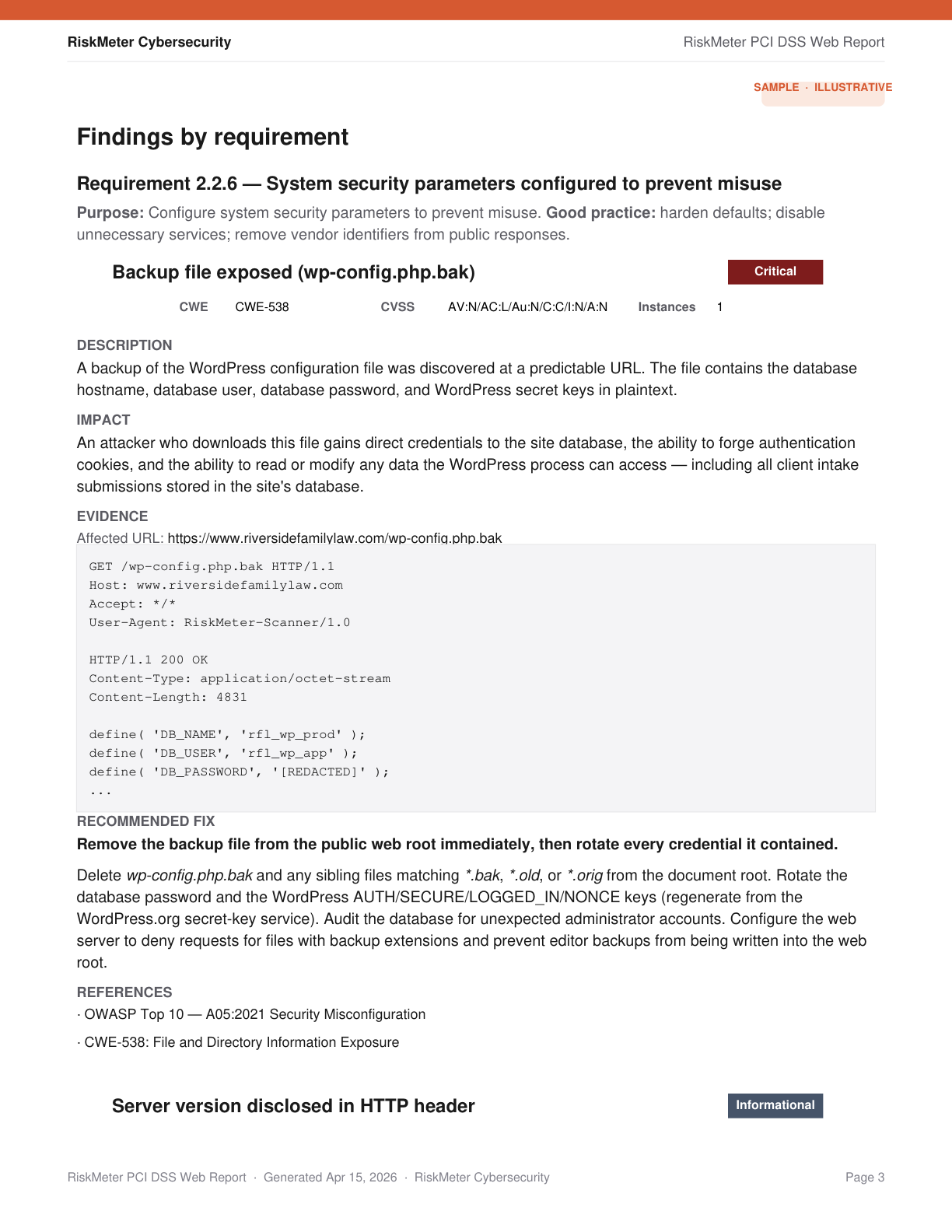
- Executive summary table of every vulnerability group with instance counts
- Suitable to attach to a cyber-insurance application
Page preview